Problems extracting FTP Session file artifacts on Security Analytics
Article ID: 168620
Updated On:
Products
Security Analytics
Issue/Introduction
FTP traffic in an extraction job is split into FTP session artifacts and file artifacts. Artifacts that show as "ftp session" are the clear text of the FTP commands (greeting message, return code, login, password, etc.). File transfers are shown separately as their file name. Certain traffic filters may result in FTP file artifacts not being extracted correctly.
Cause
Extractor needs to see both FTP control sessions (port 21) and the file transfer sessions, which can be conversations on other TCP ports. If the filter is set to to "tcp_responder=21", FTP traffic can be located in Summary or Reports, but only the control sessions on port 21 will be displayed, not file transfers.
Resolution
Once the FTP traffic has been located (for example, using tcp_responder=21), set the time frame to contain the required FTP session(s), and clear out the filter. If needed, filter further to specify the desired traffic using source or destination IP or other parameters, but do not filter on TCP port.
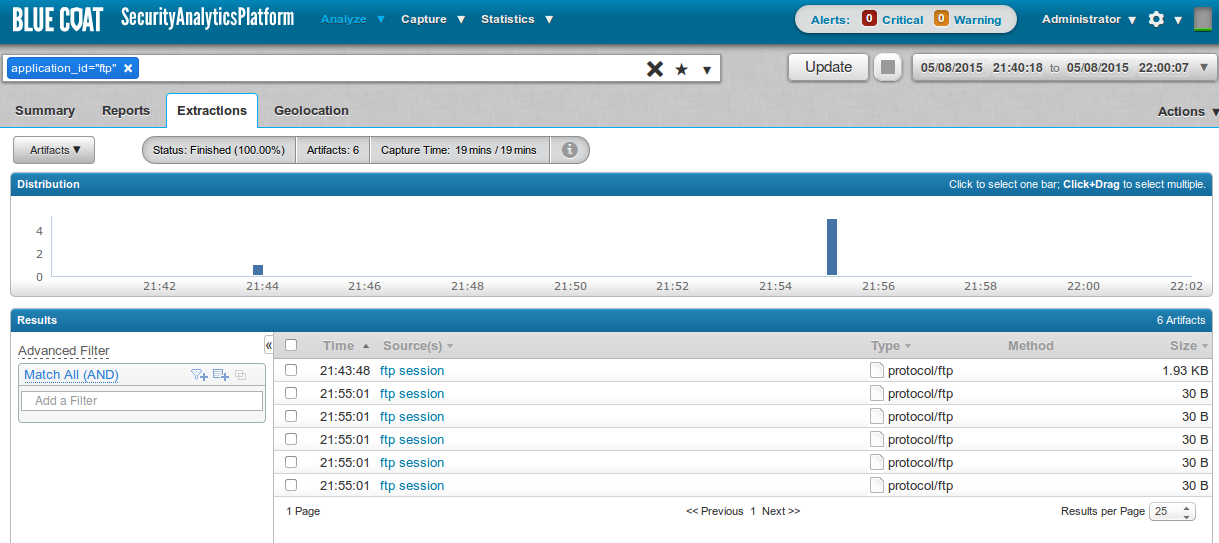
If application_id="ftp" is added to the filter, and an extraction is then run, only the ftp control sessions will be displayed in the artifacts list. These artifacts may be previewed to see the text content of the control session.
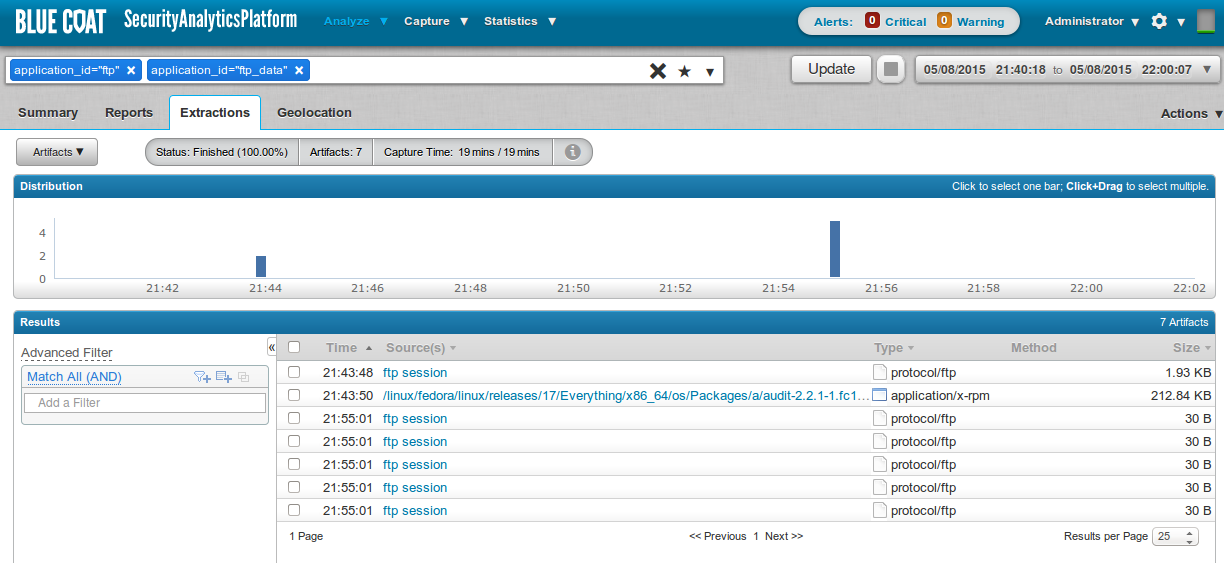
If the term application_id="ftp_data" is also added to the filter, any file transfer sessions will also be displayed. (Not all FTP connections are used to transfer files.)
Note:
Without seeing the FTP control sessions, extractor cannot determine what other traffic contains the FTP file transfers. Therefore, application_id="ftp" is always required in conjunction with application_id="ftp_data" in order to see the files for extraction.
If application_id="ftp" is added to the filter, and an extraction is then run, only the ftp control sessions will be displayed in the artifacts list. These artifacts may be previewed to see the text content of the control session.
If the term application_id="ftp_data" is also added to the filter, any file transfer sessions will also be displayed. (Not all FTP connections are used to transfer files.)
Note:
Without seeing the FTP control sessions, extractor cannot determine what other traffic contains the FTP file transfers. Therefore, application_id="ftp" is always required in conjunction with application_id="ftp_data" in order to see the files for extraction.
Feedback
Yes
No
